Identity at the center of Zero Trust
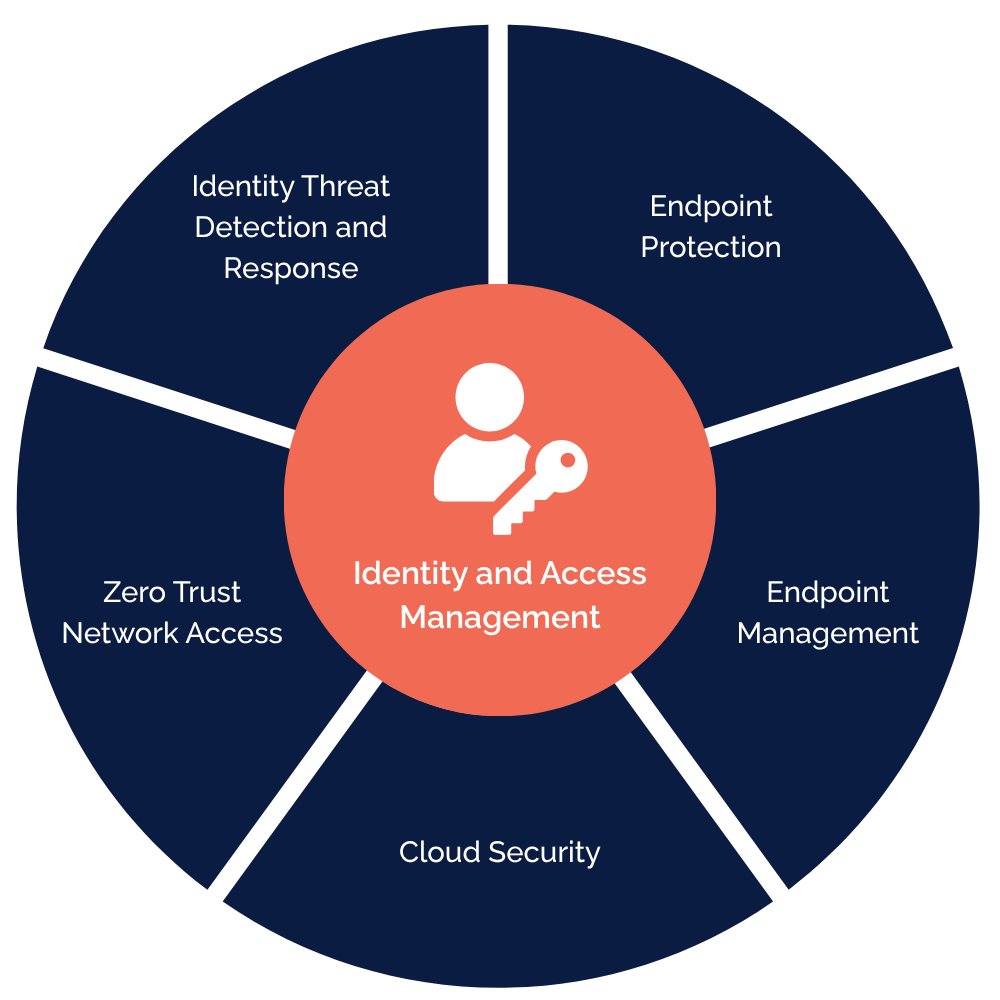
Identity and Access Management (IAM) sits at the center of modern security, helping connect visibility, control and trust across cloud, devices, applications and users.
Why Zero Trust matters
Traditional security models were built around the idea of trust inside the network perimeter. That model no longer fits modern environments where users work across locations, devices connect from many contexts, and business-critical resources live across cloud and on-prem environments.
Zero Trust replaces broad access and static assumptions with access decisions based on identity, context, device trust and risk.
Zero Trust Security in practice
Zero Trust is not one product or one control. It is an approach that brings identity, access, devices and visibility together to create stronger control across the organization.
Identity and Access
Identity underpins Zero Trust by defining who gets access to what, under which conditions and with what level of privilege.
Device trust and endpoint management
Zero Trust requires trusted devices. Endpoint management keeps devices configured, updated and secure for controlled access.
Zero Trust Network Access
ZTNA limits access to specific resources based on identity and context, shrinking the attack surface and enforcing least privilege.
Identity Threat Detection and Response
ITDR spots and responds to attacks on identities, credentials and privileged access, improving visibility into identity-based threats.
Cloud visibility and policy enforcement
Zero Trust depends on clear visibility across cloud environments. Strong controls help reduce misconfigurations and enforce policy more consistently.
Privileged access and least privilege
Zero Trust limits access to only what is needed, reducing exposure and tightening control over sensitive accounts, roles and systems.

Connected control strengthens Zero Trust and compliance
Zero Trust works best when identity, access, devices and cloud controls work together. Connected control helps reduce blind spots, strengthen policy enforcement and support continuous compliance across SaaS, cloud and on-prem environments.
Are your security investments working together?
We help define a clear roadmap toward Zero Trust Security built on identity.
Advisory and maturity assessment
We assess your current identity and security landscape, identify gaps and clarify where Zero Trust can create the most value.
Zero Trust architecture and roadmap
We define practical roadmaps and architecture priorities for Zero Trust built on identity, aligned with your environment, risk profile and business needs.
Implementation across identity-led controls
We support implementation across identity, access, governance, privileged access and related Zero Trust technologies.
Ongoing support and continuous improvement
We help strengthen Zero Trust over time through continuous improvement, operational support and practical guidance across evolving environments.
FAQ
Zero Trust is a security approach that removes implicit trust and replaces it with access decisions based on identity, context, device trust and risk. It helps organizations reduce unnecessary access and strengthen control across users, devices, applications and cloud environments.
Zero Trust supports compliance by improving visibility, strengthening access control and reducing gaps across SaaS, cloud and on-prem environments. With continuous control and policy enforcement, organizations are better equipped to support compliance in fast-changing environments.
Identity sits at the center of Zero Trust because it helps determine who gets access, under which conditions and with what level of privilege. A strong identity foundation makes it easier to enforce access policies, support least-privilege access and respond to changing risk across the environment.
Cloudworks helps organizations define, design and strengthen Zero Trust architectures with identity at the core. With deep IAM expertise, we help connect identity, access, governance and security controls into a clearer and more resilient approach.
 Ready to explore your Zero Trust priorities?
Ready to explore your Zero Trust priorities?
Book a short introduction meeting to discuss how Cloudworks can help you define the right next steps.




